Have you guys ever been browsing your favorite website or playing an online game and all of a sudden, the stream starts to be all shaky, and your connection seems slow as a snail. You might quickly go and try another website on the browser only to find every other website loads just fine, but the one you want to surf – those %$@%^s need to upgrade their server connection? (So, you think), but what may actually be a totally different scenario is that the website is likely being hit by a Denial of Service Attack.
Well, unusually high traffic can also make a website server load slow for you, but in most cases, if the slowness is persisting for a little more than comfortable, it may be a Distributed Denial of Service (DDoS) Attack.
Such was the same case with one of our clients on 17th January 2017. Just as he was about to checkout after ordering a Local SEO Pack from our website, BOOM! The website got stuck, and then came the “white-screen-of-nothingness.”
Alike every other unaware visitor, Andrew (I am sure he won’t mind) was a bit frustrated with the experience. And the next moment he was writing a tantrum in Gmail, complaining about how we should upgrade our Servers and get more capacity for traffic, and how our website sucked!
Rest assured Andrew; we surely don’t run our company on shared environments. Sharanyan Sharma, our founder wasn’t too surprised to receive the email, as just at that moment we were hit by a Layer 4 (Syn Flood) DDoS Attack, the size of 6.2 GBpS. To read more about our experience and how we tackled it click here.
And that was our 2nd DDoS Attack in the last 4 years. The first one we faced wasn’t any close to this magnitude. But 6.2 GBpS, I tell you this is pretty freaking BIG.
Since the past decade, Denial of Service attacks have been on the rise. Experts say, that such attacks in any magnitude cannot be fully stopped, as you can never truly find and control the core of these attacks, but the damaged can be minimized by taking controlled measures and letting Denial of Service Mitigation Experts handle the situation.
And when I say, Mitigation Experts, I am not in any way referring to Cloud Flare, I am talking Incapsula, Arbor, Verisign, Nexusguard. You get the drift. These folks charge $10000s by the hours (for starters). We have tried quite a few Mitigation Services, and one thing we can conclude is that there is nothing called Cheap DDoS Mitigation. You either get someone good and pay for it, or do not bother at all.
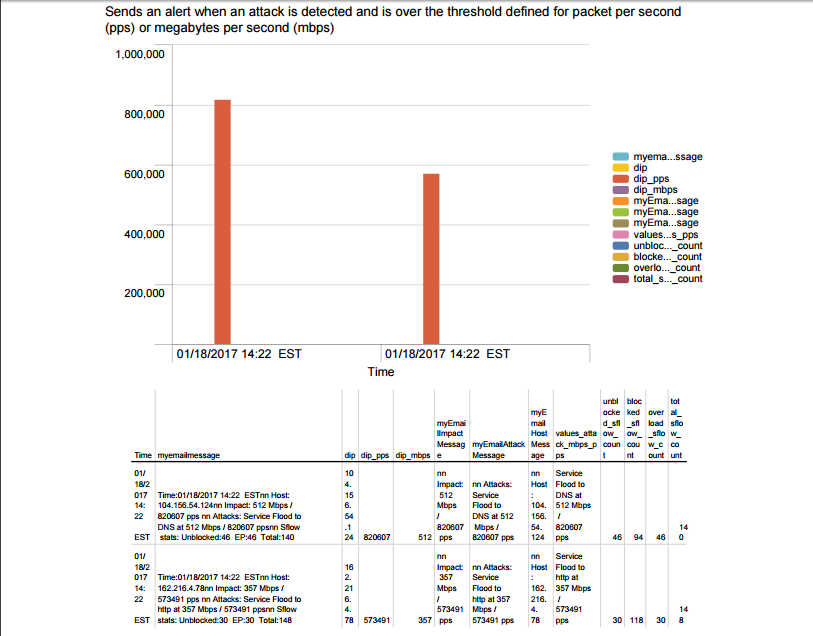
DDoS Alert Report from Splunk (primeone.global Impacted January 2017)
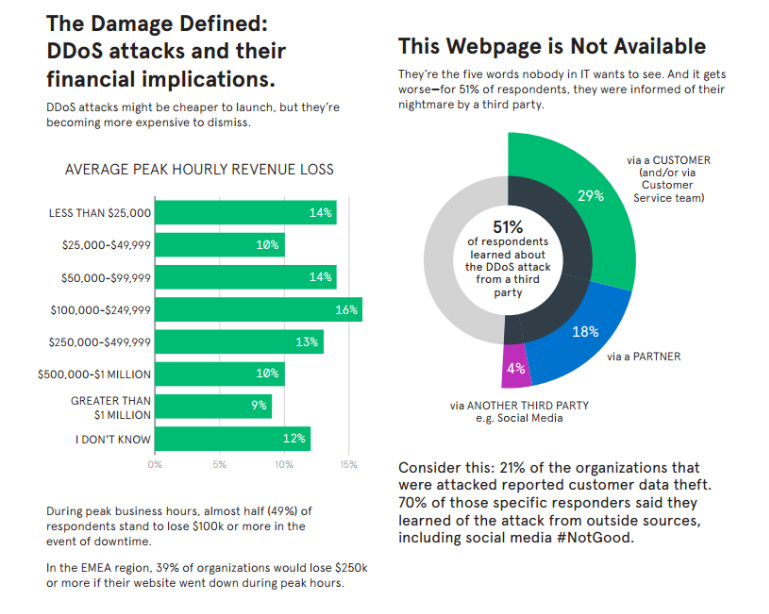
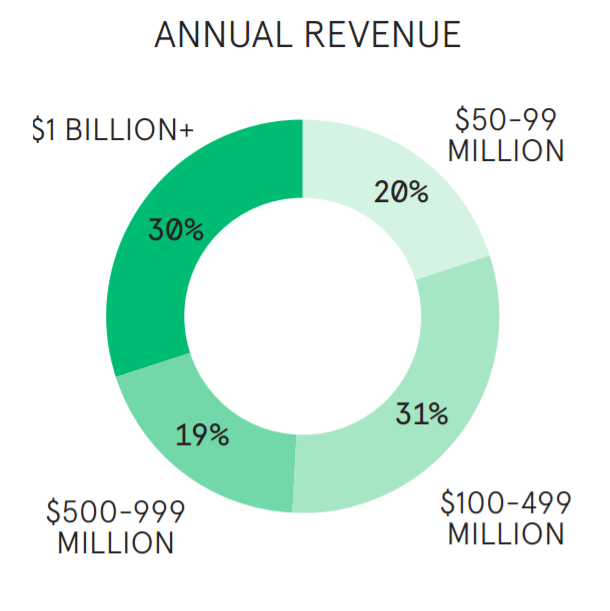
We looked at the Cyber Security and Risks Threat Survey of Arbor, Neustar, Kaspersky and Incapsula only to find very strict similarities in their research. Neustar has conducted research amongst 1000s of managers, directors, CTOs, CSOs, CISOs and other chief executives to understand the impact of Denial of Service Attacks on their organization and what measures they are taking to mitigate such attacks.
The majority of these respondents belong to the IT, Finance or Retail Industry. The respondents taking part in these surveys accrue anywhere from $100M to $1B per year. For these companies the risk picture is magnanimous. The cost of an hourly downtime for such organizations ranges anywhere from $100,000 to $500,000 subject to peak traffic and sales seasons.
Global Data at a Glance
- 73% of all organizations interviewed suffered a DDoS attack.
- 85% of attacked organizations were subjected to multiple DDoS attacks.
- 44% of attacked organizations were hit six or more times.
- 49% of respondents would lose $100k or more per hour during peak periods due to a DDoS attack.
- 33% would lose $250k or more during the same periods.
- 76% of organizations are investing more in response to the threat of DDoS attacks.
- 38% are investing more in DDoS defence, but acknowledge the investment should be even greater.
- 39% of respondents took three or more hours to detect a DDoS attack.
- 25% detected the DDoS attack between three and five hours.
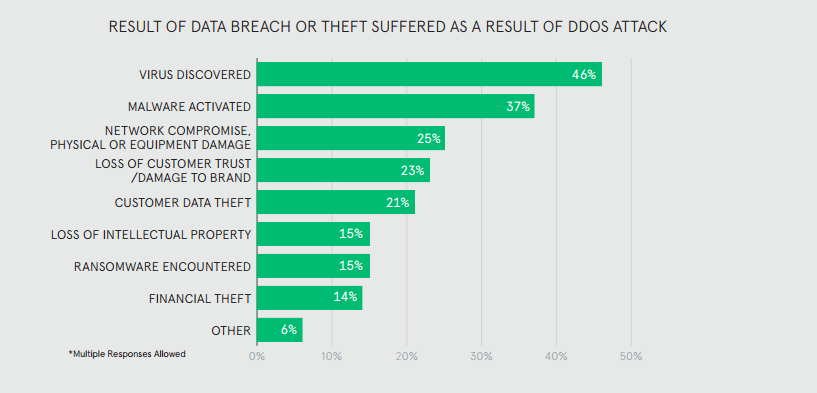
- 53% of attacked organizations were breached as a result of a DDoS attack.
- 46% reported finding a virus after the breach
(Source Neustar 2016 DDoS Report)
In their IT Risks Survey Thread of DDoS Attacks survey report, Kaspersky states:
20% of companies with less than 50 employees have been a victim of DDoS Attack at least once in their lifetime. The top three Industries affected by DDoS Attacks, are not surprisingly, IT, Financial Services and Telecommunications.”
DDoS Attacks cost a lot of businesses. Apart from financial loss and business downtime, more than two-thirds of DDoS Attack victims have reported another type of security threat directly coinciding with the main attack. (Thankfully, we belong to the one-third). Although DDoS Attacks don’t say and happen and are enough to take large scale websites down, combining such attacks with other security intrusions only helps to multiply the collateral damage, apart from the significant loss of business downtime and reputation.
In the Worldwide Infrastructure Security Report, Arbor states…
- There is a steady growth in the size of DDoS Attacks YOY. In 2015, 20% of service based companies reported attacks, an average of 50Gbps. In 2016, nearly 33% of Service providers reported attacks the size of 100Gbps on average. Which only means to say that the top-end size of these attacks is nearly doubling every year.
- The largest attack in 2016 reported 1 TBPS. Octave Klaba, the founder of OVH, reported in a Tweet.
@Dominik28111 we got 2 huge multi DDoS: 1156Gbps then 901Gbps pic.twitter.com/NyFTr6KLCC
— Octave Klaba / Oles (@olesovhcom) September 19, 2016
The tweet exclaims there were simultaneous attacks the size of 100 Gbps on OVH, which totalled more than 1TBps. And the largest single attack on OVH peaked at 799 Gbps and 93MBps.
- In the majority of the cases, Customers are the number target for DDoS Attacks.
- The proportion of survey service provider respondents noticed cloud-based attacks, which have grown from 19% in 2012, to 29% in 2014 and 33% last year – again a clear trend.
- Amongst the different types of Attacks, Application Layer Attacks seem to be the most popular at 93% in 2016, a significant rise from the 90% is 2015 and 86% in 2013.
- The most common service targeted by these Application Layer Attacks is DNS, which hasn’t been much targeted
- The most common top motivation behind criminals giving DDoS Attacks is “to show-off their attack capabilities,” with the second and third most common reason being “gaming” and “extortion.”
- A growing proportion of respondents claim that they are noticing malware and virus, along with Data theft after DDoS Attacks, which means to say that these attacks are being done merely as a means of distraction.
- There is also a significant growth in SIP/VoIP based attacks, which is up from 9% in 2015, to 19% in 2016.
Increased interest in DDoS Mitigation and Detection Services continue this year due to these ever-increasing attacks.
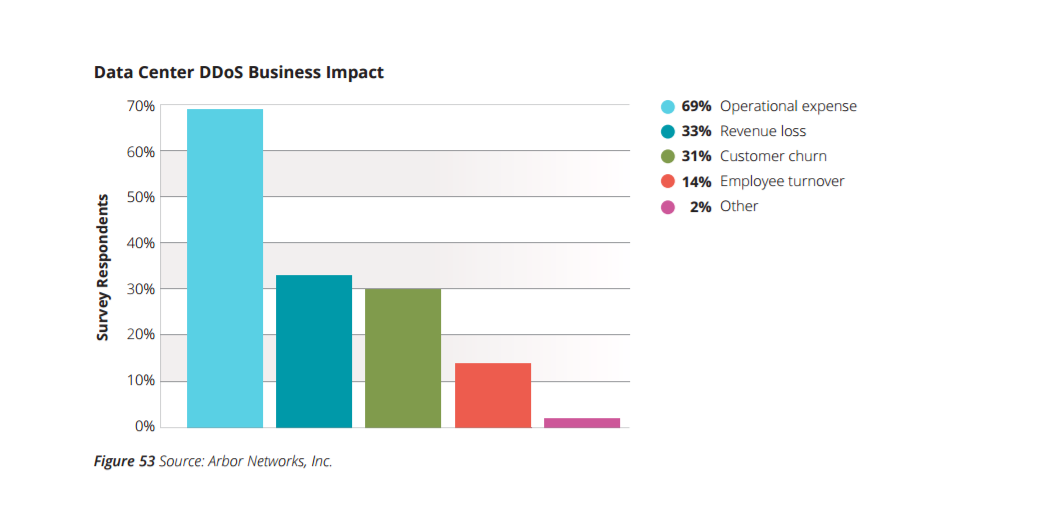
DDoS Attacks can cause even more damage if organizations aren’t prepared. 74% of the respondents in the Arbor survey claimed that they were spending more on Mitigating the attacks than their overtime loss due to the attacks, and even acknowledged that they needed to pay more to better handle such attacks. Therefore, the number one business impact due to DDoS is increased operational expense, followed by Revenue Loss, Customer Churn, Employee Turn Over and others. See image below.
Time Is Money, And Money is the Game!
The harsh truth is that, nobody can afford a Successful DDoS Attack and neither anybody can mitigate a DDoS Attack complete – well, at least an attack of that stature.
Increasingly, DDoS Attacks are being deployed in conjunction with other illicit activities in order to distract or misguide organizations on the actual motive of such attacks, which is usually to install malware, ransomware or viruses.
After the Storm
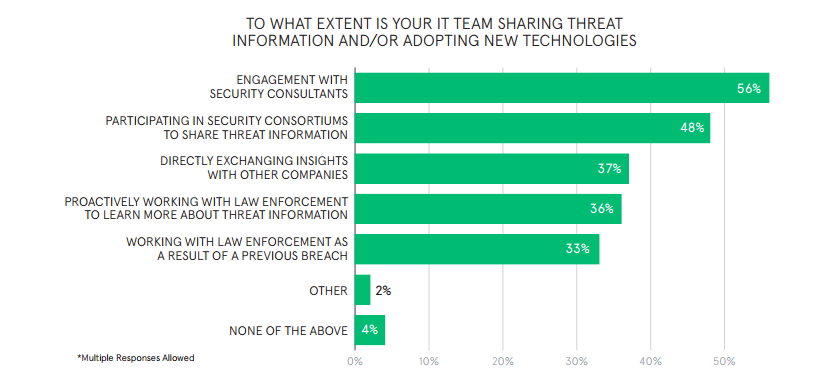
The aftermath of the storm leaves behind a strong sense of vulnerability, that nobody on the Internet is safe. Where some organizations are turning to one another for guidance and exchange of information, others are taking refuge in the comfort of Security Consultants and a majority of these organizations are working in conjunction with Law Enforcement to get to the root of these attacks in lieu of previous attacks or to simply ward of impending attacks.
Before You Go!
All data sources point to one and only one fact. 2017 is already witnessing a multitude of DDoS Attacks around the globe, and these attacks will only continue to increase as time passes.
“It is not about when these attacks will happen, it is about HOW MANY TIMES.”
Taking into account the new type of smokescreen attacks, Denial of Service has started resembling ransomware attacks more than anything else. SMBs are the ones that suffer the most under the pressure of such attacks, and the technology behind such attacks is Simple, but the measures to fend them are complex and resource-intensive.
The average financial damage of a DDoS is quite significant, which still turns out to be less than the cost of mitigating such attacks. So, most Small Media Businesses that have spent money on DDoS Mitigation services claim that they would rather strengthen the security of their infrastructure to prevent a data breach than spend more money on mitigating these never-ending attacks.
Has your organization faced a DDoS attack in the last 12 Months? If so, how bad was the attack and what are you doing to wade off such attacks from happening in future? Data security is a big concern and we would surely love to know what and how you are tackling these unfortunate events.